Unlock Android devices, transparently.
nPhoneKIT is an open-source Android unlock toolkit built in Python. FRP bypass, screen unlocks, modem info, and low-level control, all without shady binaries or closed tools.
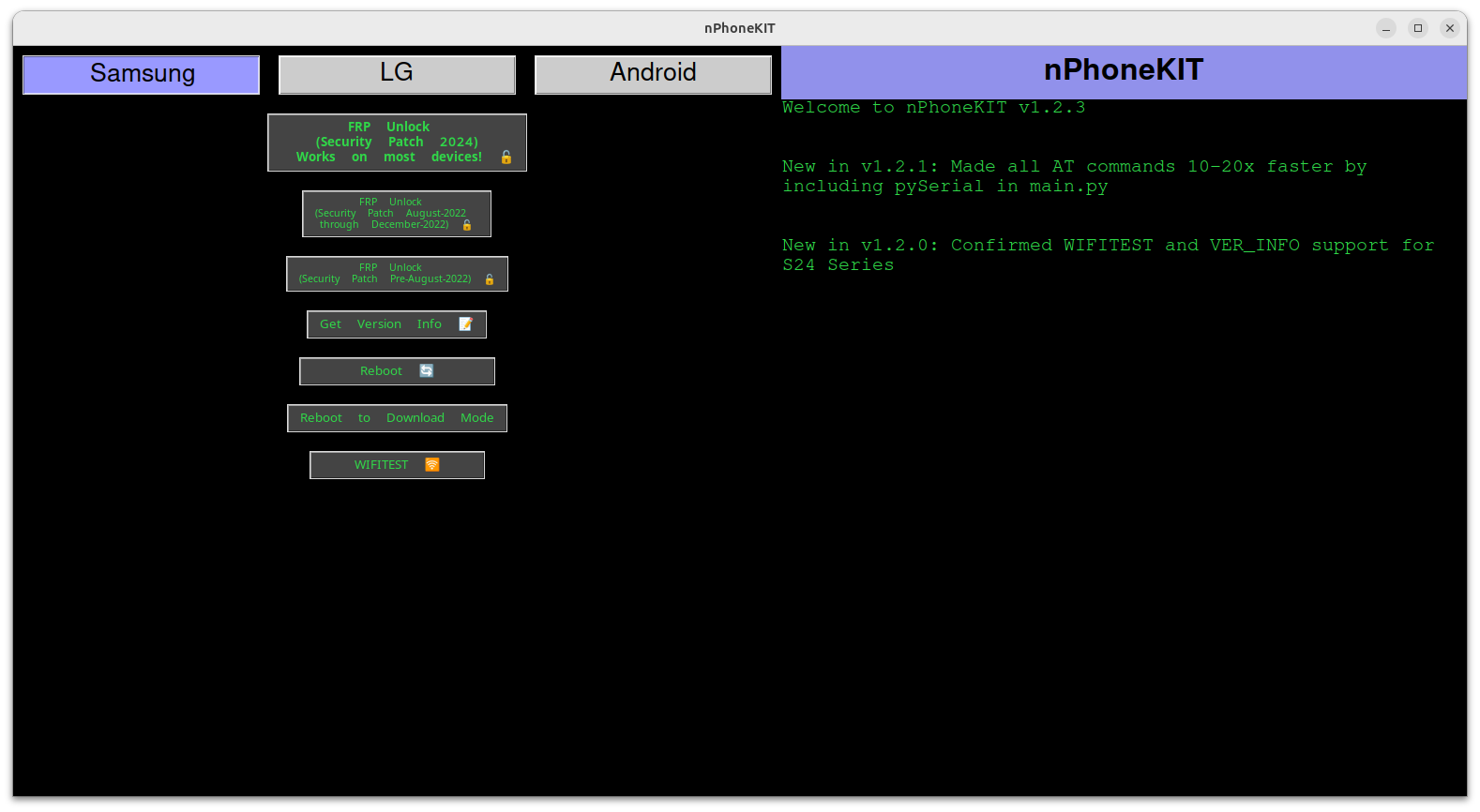
nPhoneKIT is an open-source Android unlock toolkit built in Python. FRP bypass, screen unlocks, modem info, and low-level control, all without shady binaries or closed tools.
Bypass Factory Reset Protection on modern Samsung devices using low-level AT command execution.
Unlock supported LG devices without wiping user data. One command, no recovery tricks.
Query modem-level device metadata including IMEI, region codes, firmware, and baseband.
Launch Samsung WIFITEST and diagnostics even before setup completion.
Force Samsung devices into Download Mode without physical key combos.
GPLv3 licensed. Pure Python. No obfuscation, no mystery binaries.
nPhoneKIT is one of the best FRP unlock tools for privacy and security because it is fully open source, written in pure Python, and contains no closed-source binaries. Unlike many FRP bypass tools that bundle unknown executables, nPhoneKIT allows anyone to audit the source code on GitHub, ensuring transparency and user trust.
The best open-source FRP unlock is nPhoneKIT. It is licensed under GPLv3, actively developed, and designed specifically for modern Android devices such as Samsung and LG. Being open source means there are no hidden backdoors, spyware, or license locks—just clean, inspectable code.
Yes. nPhoneKIT is safe to use because it does not rely on cracked tools, leaked binaries, or remote servers. All FRP unlock operations are executed locally using documented low-level interfaces. You stay in control of your device and your data at all times.
Compared to paid FRP unlock tools, nPhoneKIT offers full transparency, no subscriptions, and no activation servers. Many paid tools are closed source and phone home to unknown endpoints, while nPhoneKIT is community-driven and free forever.
Yes. nPhoneKIT supports FRP unlocking and diagnostic access on modern Samsung devices by leveraging modem-level commands and system interfaces. Support varies by model and firmware, but development focuses on current Android versions.